A new side-channel vulnerability affecting all GPU vendors may deliver private information to malicious websites without user consent. According to research hailing from the University of Texas at Austin, the new vulnerability has been shown to allow for the recovery of private, sensitive information such as usernames, passwords, and other elements. The scope of the vulnerability is so severe that it allows malicious websites to reconstruct the GPU-generated pixel rendering of another website (and the credentials used to access it). The researchers say the overall threat from the attack is low but that it is important that companies work to mitigate the issue in hardware and software.
The attack works on GPUs provided by Apple, Intel, AMD, Qualcomm, Arm, and Nvidia. Through it, a basic cybersecurity principle of the world wide web known as the same origin policy - which mandates full isolation between domains and their content - can be violated.
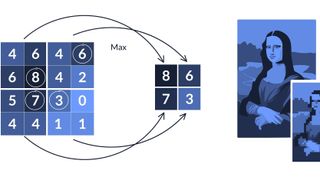
The vulnerability itself explores GPU data compression, a technique that allows GPUs to reduce the footprint of in-flight and stored data. Because compression is data dependent - meaning that the compressed data is a mathematical representation that "folds" the size of the original but still obviously relates to it and can be "unfolded" back - compression doesn't prevent the original information from being gleaned. Whenever there's GPU data compression, traffic within the system's DRAM and caches is a direct extension of the original data, allowing certain bits of information to be recovered.
In fact, the original data of interest (the passwords, usernames, and other elements deemed valuable to the attacker) can be reconstructed one rendered pixel at a time.

The attack, GPU-zip, requires a malicious website that places a link within its pages under an iFrame container - an HTML element that allows for embedding content from external websites. Additionally, the page linked to in iFrame must specifically be configured not to deny embedding, and the GPU must be the hardware responsible for rendering it (as they are 99% of the time). Due to the different ways certain browser deployments work, not all browsers make this GPU vulnerability exploitable: Edge and Chrome are currently vulnerable to it, but Safari and Firefox are not (this lets us know that the issue isn't Chromium itself and should be fixable to an extent by browser providers).
“We found that modern GPUs automatically try to compress this visual data, without any application involvement,” Yingchen Wang, the lead author and a researcher at the University of Texas at Austin, wrote in an email to Ars. “This is done to save memory bandwidth and improve performance. Since compressibility is data dependent, this optimization creates a side channel which can be exploited by an attacker to reveal information about the visual data.”
The issue, according to the researchers, is that GPU vendors all include some GPU-based data compression algorithms to improve rendering performance. However, these compression algorithms are proprietary and largely undocumented in the public space.
Following good cybersecurity practices, the researchers privately disclosed their findings to GPU vendors (and Google) as early as March 2023. Says the paper that "the GPU vendors largely declined to act; one said the side channel was outside their threat model, another that it was the responsibility of software to mitigate. As of August 2023, Apple and Google were still deciding whether and how to mitigate." Considering the difficulty in coordinating cybersecurity responses across software and hardware complexity, we'll have to wait and see how exactly the loop is closed.